PROOF
Operational evidence from live telecom deployments
These technical briefings and operational deployment examples show how communication identifier governance operates across live telecom environments.
The material demonstrates lifecycle governance, operational validation and control boundary enforcement across carrier, platform and enterprise environments.

ARCHITECTURE
Operational governance briefings
Operational governance patterns are emerging across numbering, messaging, routing, eSIM and AI-driven communication environments.
The following briefings explore how communication identifier governance applies across increasingly programmable telecom and enterprise execution systems.
OPERATIONS
Operational governance in live environments
Operational governance patterns are increasingly emerging across telecom, platform and enterprise execution environments.
The following briefings demonstrate how communication identifier governance applies across lifecycle validation, routing authority, operational coordination and execution readiness in live telecom environments.
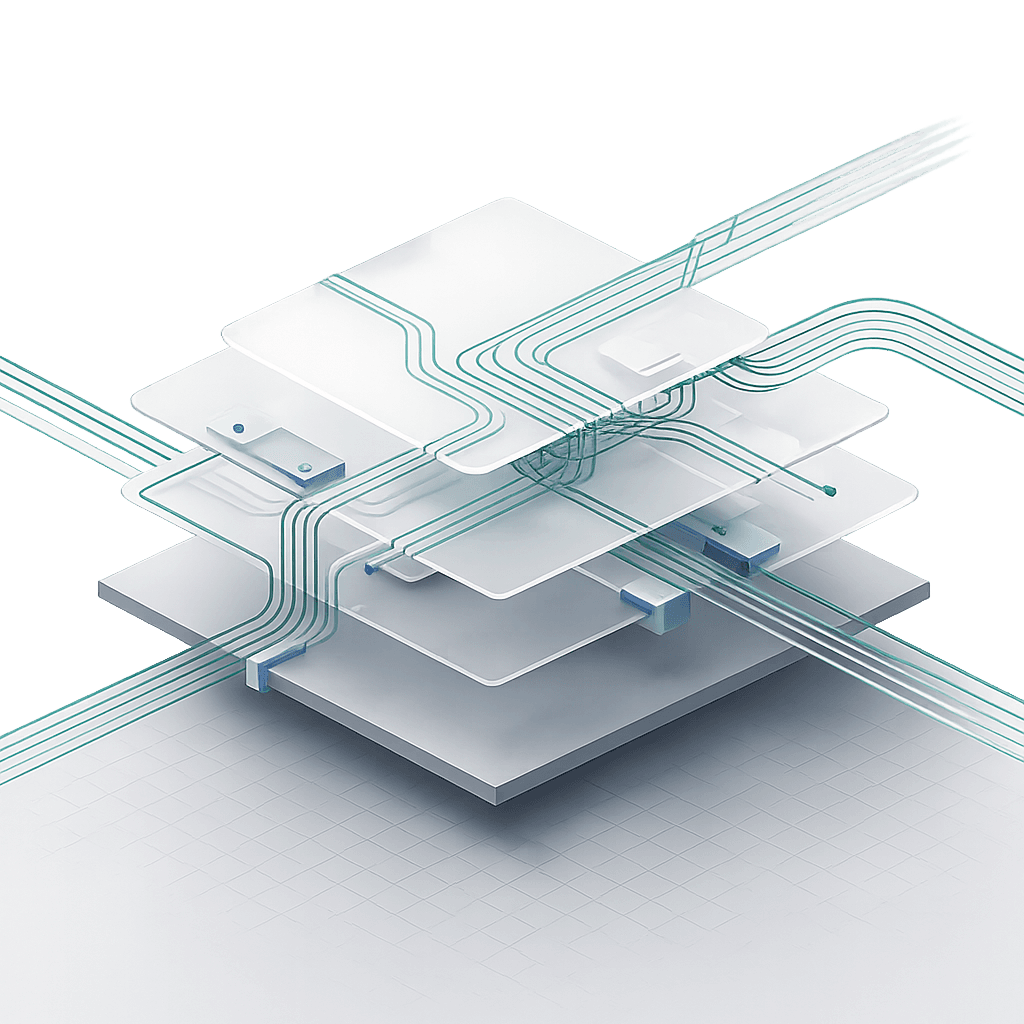
OPERATIONAL CONTROL
Pre-execution validation
Provisioning workflows validate identifier authority, lifecycle state and policy conditions before execution occurs.
If validation fails operational execution does not proceed.


Workflow validation
Automation cannot proceed until operational conditions are validated.
Execution rights derive from verified state, not inferred environment data.
Operational State Transparency
Every operational decision is recorded with policy evaluation and operational evidence.
Governance records provide operational transparency across systems and stakeholders.

RISK
Why this reduces operational risk
Deterministic
execution
Execution occurs only against validated identifier state.
Audit-ready operational
state
Operational decisions are recorded with auditable governance evidence.
Validated execution before
activation
Services activate only after identifier authority is verified.